Here you will find answers to TCP/IP Model & Operation Questions
Question 1
An inbound access list has been configured on a serial interface to deny packet entry for TCP and UDP ports 21, 23 and 25. What types of packets will be permitted by this ACL? (Choose three)
A. FTP
B. Telnet
C. SMTP
D. DNS
E. HTTP
F. POP3
Answer: D E F
Explanation
The access list denies packet entry for TCP & UDP -> all the services on ports 21, 23 and 25 are disabled. Services on these ports are FTP (port 21), Telnet (port 23), SMTP (port 25). Other services are allowed so D E F are the correct answers.
Question 2
What are two characteristics of Telnet? (Choose two)
A. It sends data in clear text format.
B. It is no longer supported on Cisco network devices.
C. It is more secure than SSH.
D. It requires an enterprise license in order to be implemented.
E. It requires that the destination device be configured to support Telnet connections.
Answer: A E
Explanation
Telnet, part of the TCP/IP protocol suite, is a virtual terminal protocol that allows you to make connections to remote devices, gather information, and run programs. Telnet is considered insecure because it transfers all data in clear text -> A is correct.
The destination device needs to support Telnet connection. For example, if a device doesn’t support TCP/IP protocol suit then maybe we can’t telnet to it.
Question 3
An administrator issues the command ping 127.0.0.1 from the command line prompt on a PC. If a reply is received, what does this confirm?
A. The PC has connectivity with a local host.
B. The PC has connectivity with a Layer 3 device.
C. The PC has a default gateway correctly configured
D. The PC has connectivity up to Layer 5 of the OSI model
E. The PC has the TCP/IP protocol stack correctly installed.
Answer: E
Explanation
The address 127.0.0.1 is called loopback address. When we ping 127.0.0.1, in fact we are testing if the TCP/IP protocol suite is installed on our device.
Note: The address 127.0.0.1 does not have anything related with the NIC card. We still ping 127.0.0.1 even if we don’t have the NIC card.
Question 4
Where does routing occur within the DoD TCP/IP reference model?
A. application
B. internet
C. network
D. transport
Answer: B
Explanation
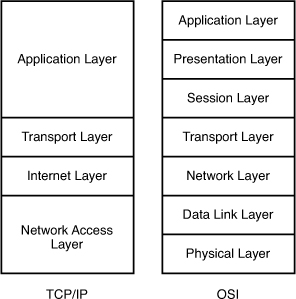
The picture below shows the comparison between TCP/IP model & OSI model. Notice that the Internet Layer of TCP/IP is equivalent to the Network Layer which is responsible for routing decision.
Question 5
A host is attempting to send data to another host on a different network. What is the first action that the sending host will take?
A. Drop the data.
B. Send the data frames to the default gateway.
C. Create an ARP request to get a MAC address for the receiving host.
D. Send a TCP SYN and wait for the SYN ACK with the IP address of the receiving host.
Answer: B
Explanation
Before sending data, the sending host checks if the destination host is inside or outside the local network. If it is outside the local network, the data will be sent to the default gateway.
Question 6
What is the purpose using the traceroute command?
A. to map all the devices on a network.
B. to display the current TCP/IP configuration values.
C. to see how a device MAC address is mapped to its IP address.
D. to see the path a packet will take when traveling to a specified destination.
E. to display the MTU values for each router in a specified network path from source to a destination.
Answer: D
Question 7
A network admin wants to know every hop the packets take when he accesses cisco.com. Which command is the most appropriate to use?
A. path cisco.com
B. debugcisco.com
C. trace cisco.com
D. traceroute cisco.com
Answer: D